BIOTECH USA - 1000g 33dosi Proteine In Polvere, protein Power, biotech Usa Gusto Cioccolato - ePRICE

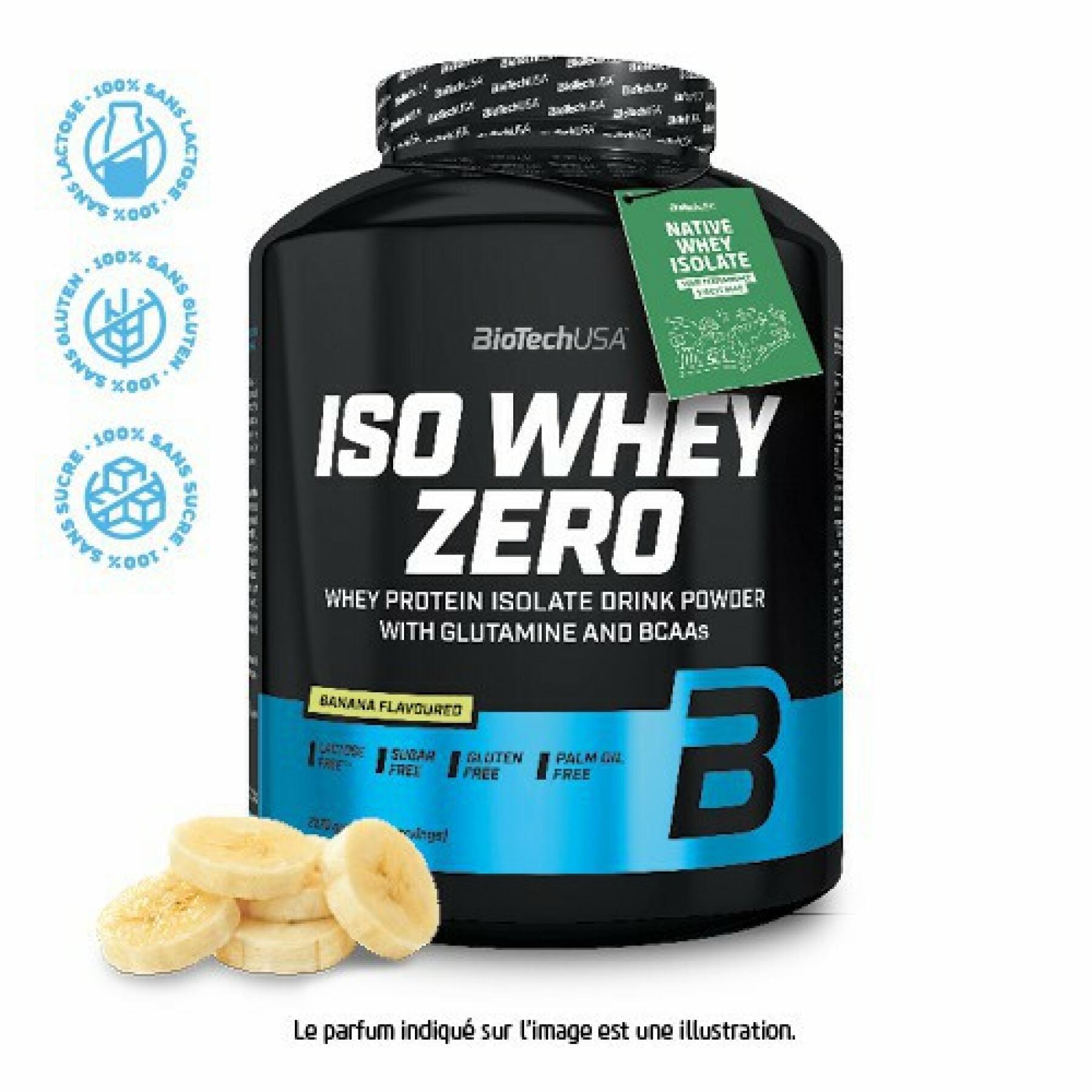
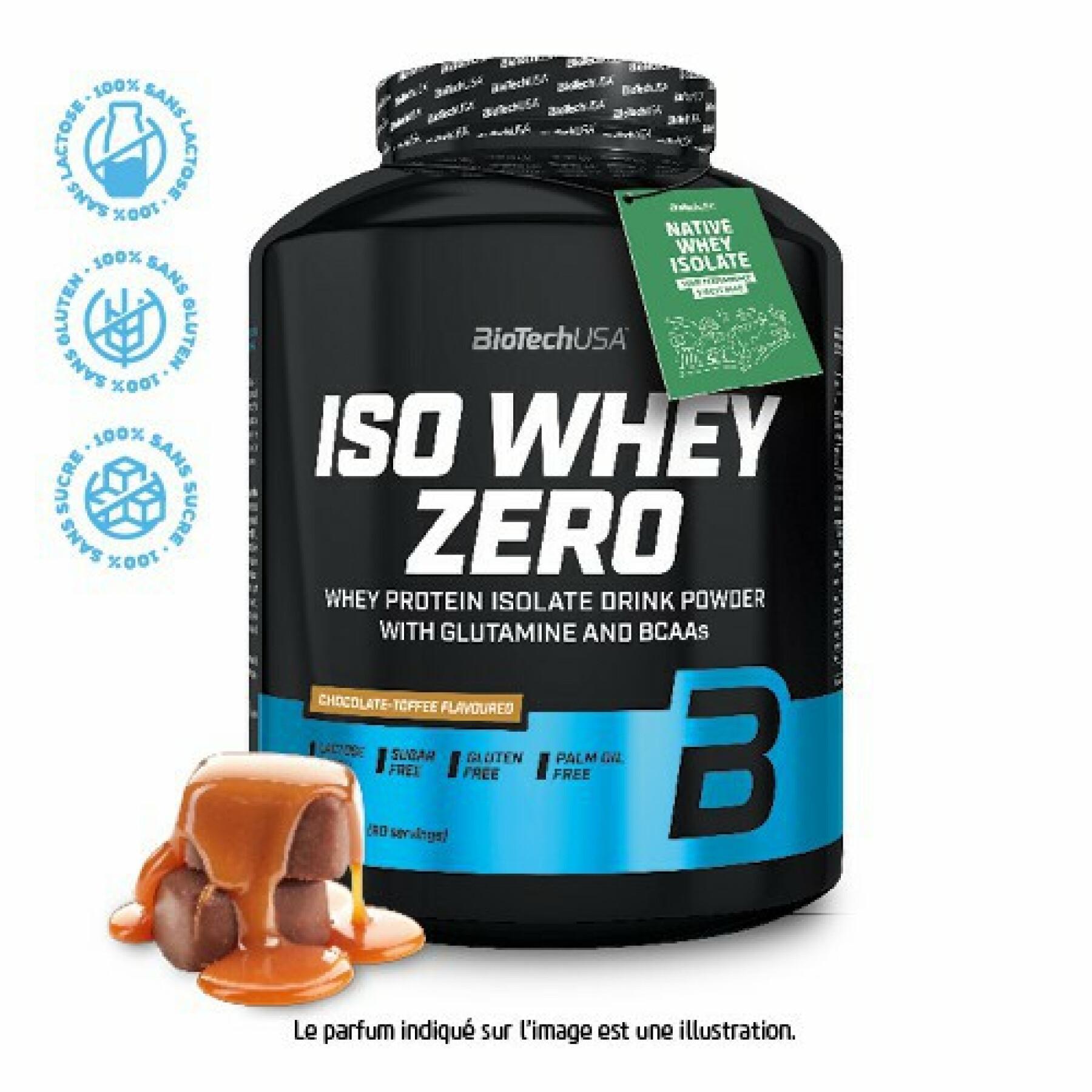
BioTechUSA Iso Whey Zero proteine isolate di alta qualità dal Native Whey Isolate, con l'aggiunta di L-glutammina e BCAA, 908 g, Cioccolato : Amazon.it: Salute e cura della persona